Russian Cyber Operations: Coding the Boundaries of Conflict

4.6 out of 5
| Language | : | English |
| File size | : | 3864 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 308 pages |
| X-Ray for textbooks | : | Enabled |
In the rapidly evolving landscape of modern warfare, cyber operations have emerged as a critical tool for nations seeking to project power and influence. Among the most active players in this domain is Russia, which has developed a sophisticated arsenal of cyber capabilities that have been deployed in a wide range of operations, from espionage and sabotage to election interference and military conflict.
This article examines the evolution of Russian cyber operations, their methods and techniques, and their impact on global security. We explore the motivations behind Russia's aggressive cyber posture and the challenges it poses for defenders. Finally, we discuss the implications of Russian cyber operations for the future of warfare and the need for international cooperation to mitigate the risks they pose.
The Evolution of Russian Cyber Operations
Russia's interest in cyber warfare dates back to the Soviet era, when the country developed a number of cyber espionage capabilities. However, it was not until the late 1990s and early 2000s that Russia began to invest heavily in offensive cyber capabilities.
In 2007, Russia established the Main Directorate of the General Staff (GRU),a military intelligence agency responsible for cyber operations. The GRU has been linked to a number of high-profile cyber attacks, including the 2007 Estonia cyber attacks, the 2014-2016 Ukraine cyber attacks, and the 2016 U.S. election interference campaign.
In addition to the GRU, Russia has a number of other government agencies and private companies involved in cyber operations. These include the Federal Security Service (FSB),the Foreign Intelligence Service (SVR),and the Ministry of Defense.
Methods and Techniques of Russian Cyber Operations
Russian cyber operations are typically characterized by their sophistication and their use of a wide range of methods and techniques. These include:
* Espionage: Russian cyber operations are often used to collect intelligence on foreign governments, businesses, and individuals. This intelligence can be used for a variety of purposes, including blackmail, policy influence, and military planning. * Sabotage: Russian cyber operations have also been used to sabotage critical infrastructure, such as power plants, water treatment facilities, and transportation systems. These attacks can cause significant economic and social disruption. * Election interference: Russian cyber operations have been used to interfere in elections in a number of countries, including the United States, Ukraine, and France. These attacks typically involve hacking into political campaign systems and releasing sensitive information or spreading disinformation. * Military conflict: Russian cyber operations have also been used in military conflict. For example, Russian cyber attacks have been used to target Ukrainian power grids and military systems.
The Impact of Russian Cyber Operations
Russian cyber operations have had a significant impact on global security. These operations have:
* Eroded trust in the global cyber ecosystem: Russian cyber attacks have shown that no country is immune to cyber threats. This has eroded trust in the global cyber ecosystem and made it more difficult for businesses and governments to operate securely online. * Increased the risk of conflict: Russian cyber operations have increased the risk of conflict between Russia and other countries. These operations have shown that Russia is willing to use cyber attacks as a tool of war. * Undermined democratic institutions: Russian cyber operations have undermined democratic institutions in a number of countries. These operations have been used to spread disinformation, interfere in elections, and attack political opponents.
Motivations for Russia's Aggressive Cyber Posture
There are a number of factors that motivate Russia's aggressive cyber posture. These include:
* A desire to project power and influence: Russia sees cyber operations as a way to project power and influence beyond its borders. These operations can be used to intimidate adversaries, disrupt their economies, and interfere in their political systems. * A belief that cyber warfare is a legitimate form of warfare: Russia believes that cyber warfare is a legitimate form of warfare and that it can be used to achieve military objectives. This belief is reflected in Russia's military doctrine, which states that cyber operations can be used to "disrupt the enemy's command and control systems, destroy critical infrastructure, and
4.6 out of 5
| Language | : | English |
| File size | : | 3864 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 308 pages |
| X-Ray for textbooks | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Chapter
Chapter Text
Text Story
Story Reader
Reader Paperback
Paperback E-book
E-book Magazine
Magazine Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Preface
Preface Synopsis
Synopsis Codex
Codex Classics
Classics Biography
Biography Autobiography
Autobiography Reference
Reference Encyclopedia
Encyclopedia Dictionary
Dictionary Thesaurus
Thesaurus Narrator
Narrator Character
Character Borrowing
Borrowing Stacks
Stacks Archives
Archives Study
Study Research
Research Lending
Lending Reserve
Reserve Journals
Journals Reading Room
Reading Room Special Collections
Special Collections Interlibrary
Interlibrary Storytelling
Storytelling Awards
Awards Theory
Theory Textbooks
Textbooks Tom Karako
Tom Karako Kate Rose
Kate Rose Luther Standing Bear
Luther Standing Bear Peter Conners
Peter Conners Ty Crandall
Ty Crandall Deb Mcewan
Deb Mcewan Jennifer Nansubuga Makumbi
Jennifer Nansubuga Makumbi Ada Petrova
Ada Petrova Catherine Ryan Howard
Catherine Ryan Howard Andrew Sean Greer
Andrew Sean Greer Sharon Nadeau
Sharon Nadeau Carina Frei
Carina Frei Gary Northfield
Gary Northfield Ann Southworth
Ann Southworth Kenneth W Langen
Kenneth W Langen Joseph Fewsmith
Joseph Fewsmith Cara Wall
Cara Wall Donna Andrews
Donna Andrews Lisa Fortini Campbell
Lisa Fortini Campbell Cathy Sharp
Cathy Sharp
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 W. Somerset MaughamFundus Autofluorescence: An In-Depth Look into Edward Gaily's groundbreaking...
W. Somerset MaughamFundus Autofluorescence: An In-Depth Look into Edward Gaily's groundbreaking...
 Albert CamusVoices From Pejuhutazizi: Uncovering the Rich Tapestry of Dakota Stories and...
Albert CamusVoices From Pejuhutazizi: Uncovering the Rich Tapestry of Dakota Stories and... Jamie BlairFollow ·3.4k
Jamie BlairFollow ·3.4k Donald WardFollow ·13.5k
Donald WardFollow ·13.5k Griffin MitchellFollow ·4.7k
Griffin MitchellFollow ·4.7k Harvey HughesFollow ·18.8k
Harvey HughesFollow ·18.8k Cody RussellFollow ·17.8k
Cody RussellFollow ·17.8k Floyd PowellFollow ·10.4k
Floyd PowellFollow ·10.4k Dan HendersonFollow ·8.3k
Dan HendersonFollow ·8.3k Avery SimmonsFollow ·11.8k
Avery SimmonsFollow ·11.8k
 Braden Ward
Braden WardFeminism's Forgotten Fight: The Ongoing Battle for...
The feminist movement has historically...
 Julio Cortázar
Julio CortázarBlue Heaven Black Night: A Literary Journey Through Love,...
In the realm of...
 Eddie Bell
Eddie BellA Journey Through Time: Exploring the Enchanting World of...
The vibrant tapestry of New...
 Lawrence Bell
Lawrence BellValiance Dragon Soul Press Anthology: A Literary Odyssey...
Step into a realm where...
 Aron Cox
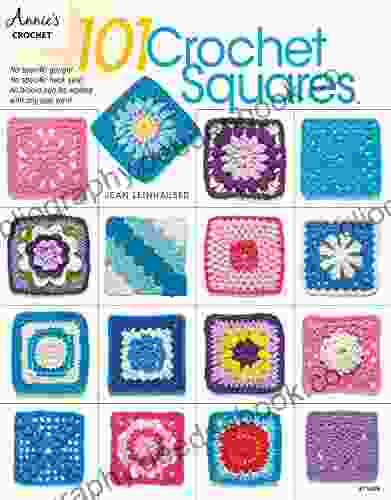
Aron CoxEmbark on a Creative Odyssey with Jean Leinhauser's "101...
Unveil a Kaleidoscope of...
4.6 out of 5
| Language | : | English |
| File size | : | 3864 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 308 pages |
| X-Ray for textbooks | : | Enabled |