Fault Tolerant Search Algorithms: Maintaining Data Integrity and Ensuring Uninterrupted Services

In an increasingly digital world, data has become an indispensable asset for businesses, organizations, and individuals alike. Maintaining the integrity and accessibility of this data is paramount to ensure uninterrupted services and prevent catastrophic consequences. Fault tolerant search algorithms play a crucial role in achieving these objectives by providing mechanisms to handle and recover from data corruption or system failures.
4.6 out of 5
| Language | : | English |
| File size | : | 8770 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 542 pages |
Concept of Fault Tolerance
Fault tolerance is the ability of a system to continue operating despite the occurrence of faults or errors. When applied to search algorithms, this means ensuring that the search operation can be completed successfully even in the presence of data corruption or hardware failures. To achieve fault tolerance, algorithms employ various techniques to detect and correct errors, handle data inconsistencies, and provide graceful degradation of functionality in the event of a failure.
Techniques for Fault Tolerance in Search Algorithms
Several techniques are commonly used to implement fault tolerance in search algorithms:
Error Detection and Correction Codes
Error detection and correction codes (EDCs) are mathematical techniques used to detect and correct errors that may occur during data storage or transmission. EDCs add redundant information to the data, which allows the algorithm to detect and correct errors up to a certain limit.
Redundancy and Replication
Redundancy and replication involve storing multiple copies of the data in different locations or on different storage devices. In the event of a failure in one copy, the algorithm can seamlessly switch to another copy to continue the search operation.
Checksums and Hashing
Checksums and hashing techniques generate a condensed representation of the data, known as a checksum or hash, which is stored alongside the data. When the data is retrieved, the algorithm recomputes the checksum or hash and compares it to the stored value. Any discrepancy indicates data corruption, and the algorithm can take appropriate action to recover or repair the data.
Consensus Algorithms
Consensus algorithms are used in distributed systems to ensure that all nodes in the system agree on the state of the data. These algorithms allow nodes to reach a consensus on the correct value, even in the presence of failures or network partitions.
Applications of Fault Tolerant Search Algorithms
Fault tolerant search algorithms find applications in a wide range of systems and applications, including:
Database Systems
Fault tolerant search algorithms are essential for ensuring data integrity and availability in database systems. They prevent data loss or corruption in the event of hardware failures, power outages, or data corruption.
Distributed Systems
Distributed systems rely on fault tolerant search algorithms to maintain data consistency across multiple nodes. These algorithms handle network partitions, node failures, and other disruptions to ensure that data remains accessible and consistent.
Cloud Computing
Cloud computing providers use fault tolerant search algorithms to ensure that data stored in the cloud is protected against hardware failures, network outages, or malicious attacks.
Data Centers
Data centers employ fault tolerant search algorithms to maintain data integrity and availability for critical business applications. These algorithms prevent data loss or corruption in the event of power failures, server crashes, or network disruptions.
Specific Fault Tolerant Search Data Structures
In addition to the general techniques described above, there are specific data structures that are designed to be fault tolerant:
Search Trees
Search trees, such as binary search trees and red-black trees, maintain a sorted order of elements and provide efficient search and retrieval operations. These trees can be modified to incorporate fault tolerance mechanisms, such as checksums or redundant copies, to ensure data integrity.
B-Trees
B-trees are a type of balanced search tree that is designed for efficient search and retrieval operations. B-trees can be made fault tolerant by using techniques such as replication or shadowing to maintain multiple copies of the data.
Bloom Filters
Bloom filters are probabilistic data structures used for efficient set membership testing. They can be made fault tolerant by using techniques such as multiple hashing functions or replication to handle data corruption or failures.
Fault tolerant search algorithms are essential for maintaining data integrity and ensuring uninterrupted services in various applications. By employing techniques such as error detection and correction, redundancy, checksums, and consensus algorithms, these algorithms provide mechanisms to handle and recover from data corruption or system failures. Understanding the concepts, techniques, and applications of fault tolerant search algorithms is crucial for system designers and developers who aim to build robust and reliable data-centric systems.
4.6 out of 5
| Language | : | English |
| File size | : | 8770 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 542 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Chapter
Chapter Story
Story Genre
Genre Paperback
Paperback Newspaper
Newspaper Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Codex
Codex Bestseller
Bestseller Library card
Library card Biography
Biography Reference
Reference Encyclopedia
Encyclopedia Dictionary
Dictionary Narrator
Narrator Card Catalog
Card Catalog Borrowing
Borrowing Stacks
Stacks Archives
Archives Study
Study Lending
Lending Reserve
Reserve Academic
Academic Journals
Journals Special Collections
Special Collections Literacy
Literacy Study Group
Study Group Dissertation
Dissertation Awards
Awards Reading List
Reading List Book Club
Book Club Kevin Ronkko
Kevin Ronkko Nh
Nh Jay Aspen
Jay Aspen Lonnie Pelletier
Lonnie Pelletier W Chan Kim
W Chan Kim Paul Bilton
Paul Bilton Angella Cooze
Angella Cooze D C Stricklin
D C Stricklin Eugene Vodolazkin
Eugene Vodolazkin Rebecca Sillence
Rebecca Sillence Walter Bagehot
Walter Bagehot Jay Althouse
Jay Althouse Tommy Keeter
Tommy Keeter Catherine Ryan Howard
Catherine Ryan Howard Kamel Daoud
Kamel Daoud Brigita Fuhrmann
Brigita Fuhrmann Rick Kemp
Rick Kemp Christopher Thomas
Christopher Thomas William I Robinson
William I Robinson Thomas Denigris
Thomas Denigris
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Gabriel BlairFollow ·16.3k
Gabriel BlairFollow ·16.3k Dwight BlairFollow ·16k
Dwight BlairFollow ·16k Dawson ReedFollow ·16.5k
Dawson ReedFollow ·16.5k Gus HayesFollow ·10.8k
Gus HayesFollow ·10.8k Edmund HayesFollow ·16.4k
Edmund HayesFollow ·16.4k Dan BrownFollow ·3k
Dan BrownFollow ·3k W.B. YeatsFollow ·13.4k
W.B. YeatsFollow ·13.4k Ismael HayesFollow ·8k
Ismael HayesFollow ·8k
 Braden Ward
Braden WardFeminism's Forgotten Fight: The Ongoing Battle for...
The feminist movement has historically...
 Julio Cortázar
Julio CortázarBlue Heaven Black Night: A Literary Journey Through Love,...
In the realm of...
 Eddie Bell
Eddie BellA Journey Through Time: Exploring the Enchanting World of...
The vibrant tapestry of New...
 Lawrence Bell
Lawrence BellValiance Dragon Soul Press Anthology: A Literary Odyssey...
Step into a realm where...
 Aron Cox
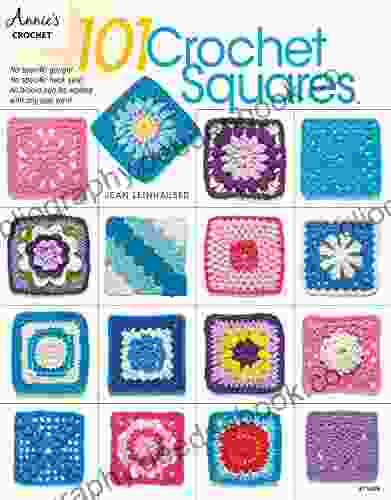
Aron CoxEmbark on a Creative Odyssey with Jean Leinhauser's "101...
Unveil a Kaleidoscope of...
4.6 out of 5
| Language | : | English |
| File size | : | 8770 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 542 pages |